Industrial Control Systems Attack and Security Measures
1. What Are Industrial Control Systems?
Industrial control systems (ICS) are systems that provide control over critical infrastructures and industrial systems. The management and control of water, energy, transportation, transmission, and other critical services are provided by ICS systems [1].
ICS systems mainly consist of Supervisory Control and Data Acquisition (SCADA), Distributed Control Systems (DCS), and Programmable Logic Controllers (PLC) components. SCADA performs the functions of automatic monitoring, control, and data collection of industrial systems. DCS includes systems used for the control of large industrial processes and consists of devices controlled from a central control room. PLCs are specialized computers used in industrial manufacturing and machinery control [2].
ICS systems have widespread usage areas. Examples of major usage areas include power plants and energy distribution networks, oil and gas pipelines, water treatment facilities, and manufacturing plants.
2. Security of ICS Systems
Since ICS systems include critical infrastructures, any problems within the systems can lead to serious dangers. For example, intentional or unintentional damage to dam or gas pipeline systems can endanger human health. Therefore, it is important to ensure the security of ICS systems both physically and in terms of software.
The first known large-scale attack on ICS systems is exemplified by Stuxnet. The Stuxnet malware, which targeted Iranian nuclear systems, disrupted the operations of nuclear facilities, resulting in serious consequences for Iran [3].
External threats are the primary threats to ICS systems. Because industrial systems directly affect human life and health, they become targets for hacktivists and terrorists [1]. Such external threats can infiltrate ICS networks using ransomware, worms, and other malicious software, leading to data leaks or even rendering the systems inoperable.
Internal threats to industrial systems arise from employees or unauthorized persons within the ICS. If system access is not properly configured, a user with access to the system can reach unauthorized areas, steal data, or damage the system. Other threats to ICS systems include improperly configured system elements, errors by inexperienced employees, natural disasters, or accidents.
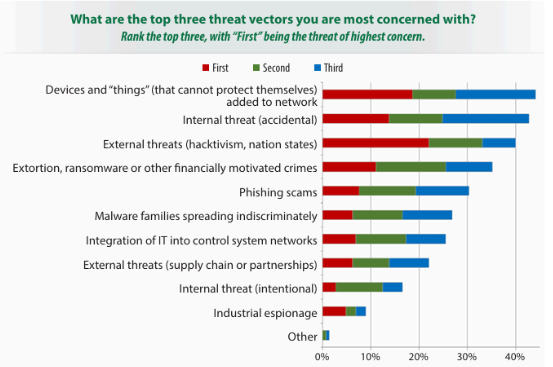
According to a report published by SANS [4], the primary threat vectors to industrial systems are devices connected to the common network. With the proliferation of Internet of Things (IoT) systems in the industry, the security of these devices has also become important. The use of IoT devices in ICS systems often requires remote access. If patch management programs are not well-configured, IoT devices, which typically use commercial operating systems, leave ICS systems vulnerable to various exploits.
Other threat vectors include internal and external threats, malware families, industrial espionage, and similar elements. The potential threat elements to ICS systems in the industry are shown in Figure 1.
3. ICS Systems Threat Actors: APT Groups
Threats to ICS systems are mostly composed of state-sponsored APT groups. Based on the report prepared by MANDIANT [5], information about some of these groups is provided below.
APT39
Also known as ITG07, Chafer, Remix Kitten. This Iran-supported APT group primarily operates in the Middle East, targeting the telecommunications, travel, and technology sectors. Their operations mostly involve monitoring, surveillance, and data theft.
In their attacks, they use a special variant of the POWBAT backdoor along with SEAWEED and CACHEMONEY backdoors. Initially, attackers infiltrate systems using spear-phishing techniques with malicious attachments or links resulting in POWBAT infections. They exploit web servers of the target organizations using web shell tools like ANTAK and ASPXSPY.
APT35
Also known as COBALT MIRAGE, Charming Kitten, G0059, Magic Hound, Mint SandStorm, Newscaster Team, Phosphorus, TunnelVision [6]. This Iran-supported cyber intelligence group targets regions including America, Europe, and the Middle East, focusing on telecommunications, media, energy, and government sectors.
Their initial activity to infiltrate target organizations involves sending spear-phishing emails. They are associated with malware such as ASPXSHELLSV, BROKEYOLK, PUPYRAT, DRUBOT, TUNNA, MANGOPUNH, and HOUSEBLEND.
APT34
Also known as OilRig, Helix Kitten, IRN2. This Iran-supported group usually targets the Middle East, focusing on sectors like finance, energy, and telecommunications.
Their attacks involve malware such as TONEDEAF, VALUEVAULT, LONGWATCH, and PICKPOCKET. TONEDEAF is a backdoor communicating with CnC addresses over HTTP or DNS, performing activities like collecting system information, uploading files, and executing shell commands. “System.doc” and “ERFT-Details.xls” are related endpoint indicators. VALUEVAULT is a compiled version of the “Windows Vault Password Dumper” tool, which steals browser credentials. It compiled using Golang, and identified by the indicator “b.exe.” LONGWATCH is a keylogger recording outputs in “log.txt” within the Windows temp directory, associated with the indicator “WindowsNTProgram.exe.” PICKPOCKET targets browser credential information, with indicators “PE86.dll” and “PE64.dll” [7].
APT33
Also known as HOLMIUM, Elfin, Peach Sandstorm. This Iran-supported APT group targets the aerospace and energy sectors, being active in regions like Saudi Arabia, America, and South Korea, particularly focusing on petrochemical manufacturing organizations.
They use malware such as SHAPESHIFT, DROPSHOT, TURNEDUP, NANOCORE, NETWIRE, and ALFA Shell. DROPSHOT, a dropper, connects to the wiper malware SHAPESHIFT. SHAPESHIFT can wipe disks, delete files, and perform other malicious activities on the system. Additionally, TURNEDUP backdoor can be dropped using DROPSHOT [8].
The group uses spear-phishing emails containing malicious HTML application files (.hta) to infiltrate target organizations’ systems.
APT31
Also known as BRONZE VINEWOOD, JUDGMENT PANDA, Red Keres, TA412, Violet Typhoon, ZIRCONIUM, Zirconium [6]. This Chinese group targets various sectors, including government, international finance, aerospace, engineering, and communications. They focus on obtaining information that provides political, economic, and military advantages.
They use malware such as SOGU, LUCKYBIRD, SLOWGYRO, and DUCKFAT. They exploit vulnerabilities in applications like Java and Adobe Flash to infiltrate target organizations.
APT10
Also known as ATK41, BRONZE RIVERSIDE, CVNX, Cloud Hopper, G0045, Granite Taurus, HOGFISH, Menupass Team, POTASSIUM, Red Apollo, STONE PANDAD, TA429, happyyongzi [6]. This Chinese APT group targets sectors including engineering, communications, aerospace, and also targets the governments of America, Europe, and Japan. They aim to obtain confidential company data to support Chinese organizations and military information to support the Chinese government.
They use malware such as HAYMAKER, SNUGRIDE, BUGJUICE, and QUASARRAT. They perform spear-phishing and network access attacks through various service providers. Spear-phishing emails include attachments with .lnk extensions, double file extensions (xxx_doc_.exe), and archive files containing malicious droppers.
APT6
This Chinese APT group targets sectors such as transportation, automotive, telecommunications, and electronics, focusing on the United Kingdom and America. They operate by stealing data.
They use malware such as BELUGA, EXCAHIN, and PUPTENT, and conduct attacks using various backdoor software used by other APT groups.
APT5
Also known as Mulberry Typhoon, MANGANESE, BRONZE FLEETWOOD, Keyhole Panda, UNC2630 [8]. This Chinese APT group targets sectors such as telecommunications, technology, manufacturing, and military technology applications, with a particular focus on telecommunications and technology companies.
They use numerous malware including BRIGHTCREST, SWEETCOLA, SPIRITBOX, Poison Ivy, and HAZELNUT.
APT3
Also known as Gothic Panda, Pirpi, UPS Team, Buckeye, Threat Group-0110, TG-0110 [8]. This Chinese APT group targets sectors such as transportation, communications, engineering, and defense. They are known for using zero-day browser-based exploits. Upon infiltrating the target system, they dump credential information, spread to other hosts related to the system, and load backdoors. Their CnC addresses are difficult to trace.
They use malware such as SHOTPUT, COOKIECUTTER, and SOGU. They conduct attacks using phishing emails, exploiting patched vulnerabilities in Adobe Flash Player’s Flash Video files. This exploit uses common heap spray techniques to bypass Address Space Layout Randomization (ASLR). The exploit also uses Return-Oriented Programming (ROP) to bypass Data Execution Prevention (DEP). The Adobe Flash Player exploit file contains shellcode along with the key used for decryption. The mentioned payload is xor encoded and stored within an image.
APT32
Also known as SeaLotus, OceanLotus, APT-C-00, Canvas Cyclone, BISMUTH [8]. This Vietnam-based APT group targets the private sector and various foreign governments and companies.
They use malware such as SOUNDBITE, WINDSHIELD, PHOREAL, BEACON, and KOMPROGO. They aim to deceive the target using social engineering methods, employing ActiveMime files containing macros that download malicious payloads from remote servers when executed.
4. Recent ICS Attack Cases
In the first half of 2024, incidents targeting industrial systems occurred in the fields of manufacturing, energy, transportation, and engineering. According to a report published by Kaspersky [9], the countries most affected by the attacks were the United States, Germany, France, Belgium, and the Netherlands, in that order. The most common methods used to infiltrate target systems were social engineering attacks and vulnerable internet access tools. Some recent industrial attack cases, utilizing information from Kaspersky’s report, are described below [10].
SideWinder Attack
The APT group known as SideWinder has carried out numerous attacks. Most of these attacks targeted new industries, primarily maritime transportation. The majority of attacks were executed through phishing emails containing Microsoft Word documents with .lnk file extensions. The attachment in the email triggers a chain of malicious software written in JavaScript and .NET. At the end of this chain, a .NET malware, which operates only in memory and can be loaded by packers, takes control of the system.
VOLTZITE Attack
The threat actor known as Voltzite targets US-based electric companies, communication, satellite services, and emergency management services. The attackers employ living-off-the-land (LOTL) techniques. LOTL, known as a fileless malware cyber attack technique, does not require any code or script to be loaded for the malware to operate. Instead, it uses tools already present on the infected system. Examples include PowerShell, Windows Management Instrumentation (WMI), and Mimikatz tools [11]. Alongside LOTL techniques, attackers also use web shells. Voltzite has obtained various data, including geographic information system data and SCADA system configurations. Some of the compromised systems include Fortinet FortiGuard, Cisco ASA, and Ivanti Connect Secure VPN.
Scaly Wolf Attacks
This group targets logistics and industrial facilities in Russia. Attackers use phishing emails to prompt the target user to download malicious files, leading to the infection of the system with the White Snake stealer malware. This malware is often found within protected ZIP archives.
White Snake, used by Scaly Wolf, first appeared on the darknet in February 2023. The stealer can operate across platforms using a Python-written downloader and can perform remote access trojan functions, including keylogging on Windows. It supports customization based on XML configuration. The attacker can execute commands on the infected machine via SSH access, utilizing the Serveo.net service to access the SSH service. The stealer can also send notifications via Telegram [11].
5. Threat Detection Mechanisms for ICS Systems
Various methods and tools are used to detect threats targeting ICS systems. Detection mechanisms can be examined under three main categories: monitoring and control tools, anomaly detection, and threat intelligence.
Monitoring and control tools include SCADA systems and SIEM (Security Information and Event Management) tools. SCADA systems are used to monitor and control industrial processes, while SIEM systems help detect abnormal behaviors by monitoring network traffic and events in real-time.
Anomaly detection involves analyzing system and user behaviors through behavior analysis. Additionally, integrating artificial intelligence and machine learning algorithms can identify behaviors deviating from the norm.
For threat intelligence, threat intelligence platforms are utilized. Threats targeting ICS systems are segregated from collected and analyzed threats, ensuring necessary actions are taken. Cyber threat intelligence, which can be used before, during, and after attacks, can be sourced internally within the organization or obtained from third-party companies.
6. Security Measures for ICS Systems
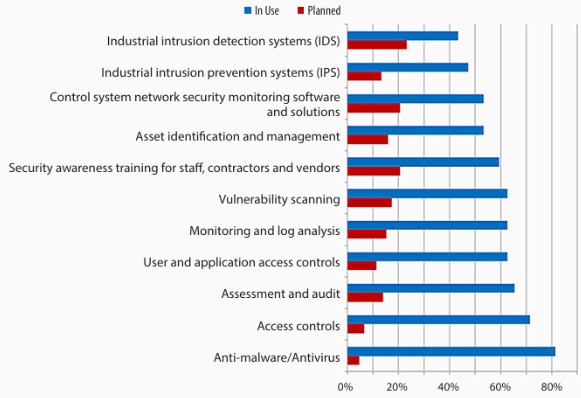
With the evolution of threats, new security solutions are needed. To ensure the security of ICS systems, solutions such as real-time monitoring, network anomaly detection, and intrusion detection systems are provided [4].
The use of firewalls that monitor network traffic is crucial for ICS system security. Alongside firewalls, using Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) are significant security measures against threats. IDS systems detect potential threats, while IPS systems automatically take action against detected threats.
Regular updates of software and hardware systems and maintaining patch management are vital for ICS system security. Each update repairs vulnerabilities in the system, making it secure. If updates are not performed, attackers can exploit discovered vulnerabilities to infiltrate the system and jeopardize it.
By separating critical systems from less critical ones, attackers’ access to the entire system can be restricted. Network segmentation between systems ensures that access to critical systems is more challenging in case of an attack.
Providing awareness training to personnel is essential for the security of ICS systems. Along with trained personnel, the presence of third-party teams regularly analyzing the system can offer additional benefits in analyzing the system externally and identifying potential threats.
Figure 2 illustrates the technologies used and planned to be used for the security of ICS systems based on the results of a study conducted by SANS [4].
Additional methods can be used to enhance the security of ICS systems. Multi-factor authentication is one example. Multi-factor authentication helps prevent unauthorized access. Periodic penetration tests and security audits can identify potential vulnerabilities and ensure measures are taken. Regularly backing up system data and preparing recovery plans for potential threats are also crucial for ICS security.
REFERENCES
1. Fortinet. (n.d.). What is ICS (Industrial Control System) security?. Retrieved from https://www.fortinet.com/resources/cyberglossary/ics-security
2. Wikimedia Foundation. (2023, October 31). PLC. Wikipedia. Retrieved from https://tr.wikipedia.org/wiki/PLC
3. İnan, Ö. (2023, August 29). Industrial Control Systems. SwordSec. Retrieved from https://swordsec.com/tr/endustriyel-kontrol-sistemleri/#:~:text=ICS%20(End%C3%BCstriyel%20Kontrol%20Sistemleri)%2C,prosesleri%20y%C3%B6netmek%20ve%20kontrol%20etmektir.
4. Gregory-Brown, B. (2017). Securing industrial control systems-2017. SANS Institute InfoSec Reading Room. Retrieved from https://paper.vulsee.com/icsmaster/doc/%E5%9B%BD%E5%A4%96/20170711_Survey_ICS_Tripwire.pdf
5. Mandiant. (n.d.-b). Advanced persistent threat (APT) Groups & Threat Actors. Retrieved from https://www.mandiant.com/resources/insights/apt-groups
6. FKIE, F. (n.d.). Malpedia (Fraunhofer FKIE). Retrieved from https://malpedia.caad.fkie.fraunhofer.de/
7. Google. (n.d.). Hard pass: Declining apt34’s invite to join their professional network | Mandiant | Google Cloud Blog. Retrieved from https://cloud.google.com/blog/topics/threat-intelligence/hard-pass-declining-apt34-invite-to-join-their-professional-network/
8. MITRE ATT&CK®. (n.d.). Groups. Retrieved from https://attack.mitre.org/groups/
9. Kaspersky ICS CERT. (2024, May 31). Q1 2024 — A brief overview of the main incidents in industrial cybersecurity: Kaspersky ICS CERT. Kaspersky Industrial Control Systems Cyber Emergency Response Team. Retrieved from https://ics-cert.kaspersky.com/publications/reports/2024/06/03/q1-2024-a-brief-overview-of-the-main-incidents-in-industrial-cybersecurity/
10. Kaspersky ICS CERT. (2024a, June 5). APT and financial attacks on industrial organizations in Q1 2024: Kaspersky ICS CERT. Kaspersky Industrial Control Systems Cyber Emergency Response Team. Retrieved from https://ics-cert.kaspersky.com/publications/reports/2024/06/10/apt-and-financial-attacks-on-industrial-organizations-in-q1-2024/
11. CrowdStrike. (2024, March 27). What are living off the land (LOTL) attacks? Retrieved from https://www.crowdstrike.com/cybersecurity-101/living-off-the-land-attacks-lotl/
