LOKI MALWARE ANALYSIS USING VOLATILITY
SHA256 hash:
0a9a1a3c031e0eb6c938510830144f26f88effe94230b1467e09123393b99650
- Summary:
This report contains a detailed analysis of a malicious software belonging to the “Loki” malware family.
A Windows 10 virtual machine was used for analysis. After running the malware on the virtual machine, the machine’s snapshot information was obtained, and the .vmem file was analyzed using the Volatility 3 tool. The obtained Indicators of Compromise (IoC) information is discussed in the report.
2. Overview of the Loki Malware Family:
Loki is a malware family focused on stealing various information such as credentials from the system. It was first detected in February 2016. It targets corporate structures especially with phishing emails. The file contained within the phishing email installs Trojan malware. The Trojan steals passwords from browsers, emails, and cryptocurrency wallets [1].
The malicious software belonging to the Loki family analyzed in this report is a stealer that infiltrates the system as an email attachment and steals information.
3. Malware Analysis:
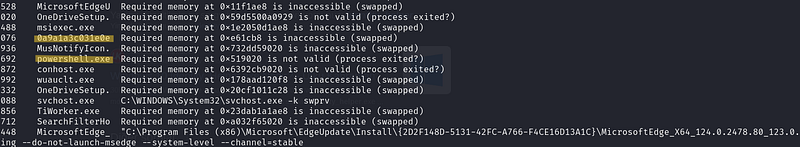
Firstly, the process tree information of the .vmem file obtained as a result of the snapshot in Volatility tool was examined. Pstree is a command that allows viewing the list of processes in a tree format.
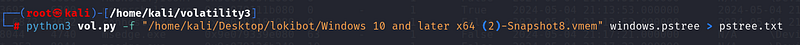
Upon examining the output of the obtained command, the exe named “0a9a1a3c031e0eb6c938510830144f26f88effe94230b1467e09123393b99650.exe” with a PID number of 8076 stands out. This is not a legitimate process name.
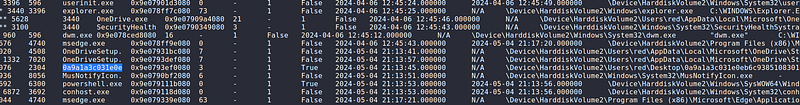
To obtain more detailed information, the cmdline command was executed to see the commands executed on the system.
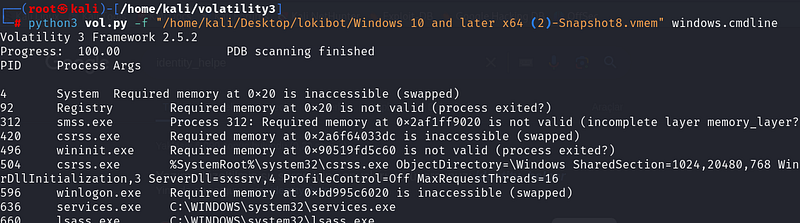
Illegal processes seen in the pstree result, followed by the executed processes and cmdline outputs, are observed. PowerShell was executed after the suspected process.
“Netscan” was used to see the network connections made on the system.
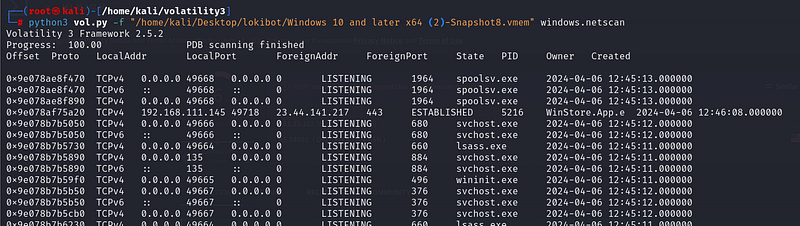

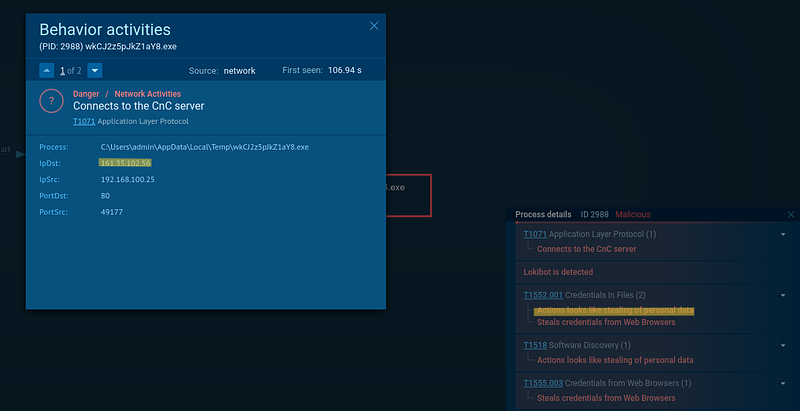
It is observed from the Netscan results that a Syn connection is sent on the three-way-handshake. The source where the connection is made may contain the suspect’s C2 (Command and Control) address. It can be checked whether it has been labeled as malicious by any vendor using VirusTotal.
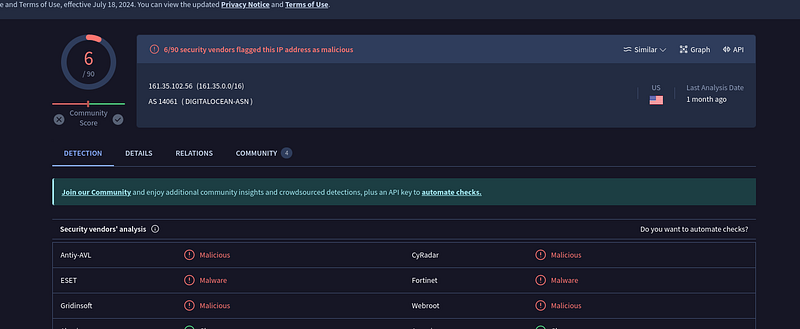
According to VirusTotal results, it has been labeled as “malicious” by 6 vendors. The suspect’s C2 address has been obtained.
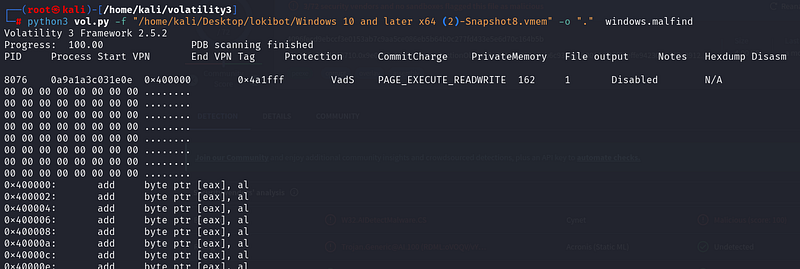
At the same time, using the “malfind” command, any hidden or injected code/DLL information on the system can be obtained. According to the results, the suspected process has been identified.
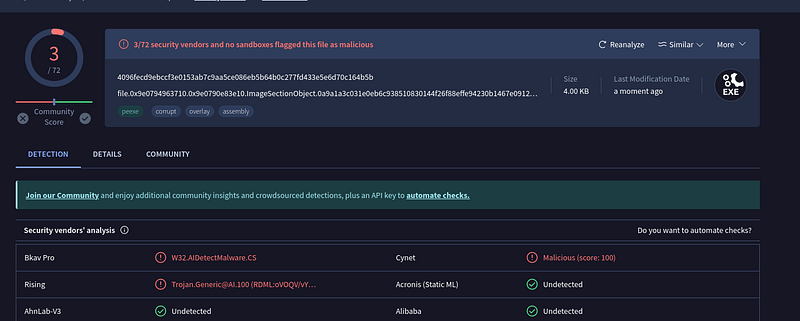
To determine the files of the suspicious process on the system, “dumpfiles” was used. According to the results, the process contains the file “file.0x9e…exe.img.”
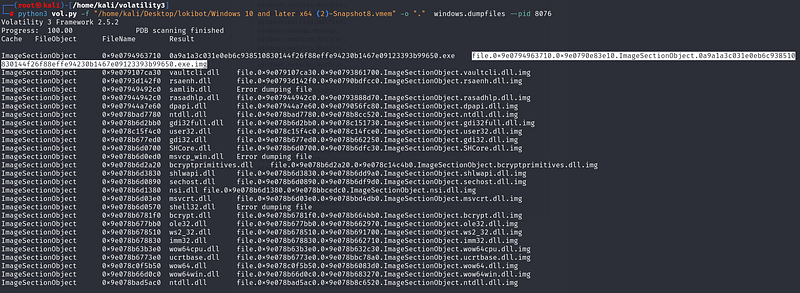
When the file is examined on VirusTotal, it is seen that it has been labeled as malicious by 3 vendors.
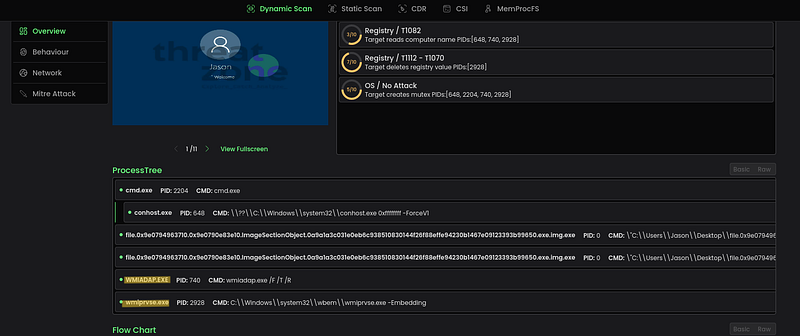
When the malicious file is analyzed on the ThreatZone sandbox, it is seen that it runs the processes “WMIADAP.EXE” and “wmiprvse.exe.” WMI Provider Host enables applications on the computer to request information about the system. It can be inferred from this that the malware is trying to obtain information about the system.
4. Conclusion:
According to the examination results with Volatility, an illegal process is running on the system. The running process then executes PowerShell, most likely establishing communication with the C2 address. According to the examination results, the file contained in the process has been classified as malicious by many providers and is trying to obtain information about the system. It operates using a stealer method attempting to steal personal data. The conclusions are verified with sandbox results. According to the results, the obtained CnC address during the analysis and the fact that the malware is a stealer have been confirmed.
- You can check AnyRun sandbox results from here: https://app.any.run/tasks/4ba470df-e682-49de-be48-8168075626e9/
5. References:
